Crowd Server is designed to provide a centralized solution for all Atlassian (Jira, Confluence, Bitbucket, Bamboo, Fisheye) and non-atlassian applications to manage users and group in one location. You can also connect multiple AD/LDAP/OpenLDAP directory to crowd to provide access to the multiple applications.
Crowd Server supports Single Sign-On(SSO) using SAML 2.0 and OpenID protocol (via OIDC1.0) that enables you to use your Crowd credentials to access any application (e.g. JIRA, WordPress, Drupal websites, etc.)
Crowd Single Sign-On(SSO) Popular Use-Cases
Crowd As Identity Provider(IdP)
miniOrange provides Single Sign-On(SSO) based plugins for Crowd supporting different protocols like OAuth, SAML for signing to client applications including WP / Joomla / Drupal / Atlassian.
Crowd As User Store
miniOrange enables Crowd Single Sign-On(SSO) with any of the SSO Protocols (SAML 2.0, OAuth 2.0, OpenID Connect, etc) using Crowd as an Identity source. This allows a user to access the application using their Crowd credentials.
Crowd As Service Provider
miniOrange IdP enables users to Single Sign-On(SSO) into Crowd. The end user first authenticates through miniOrange IdP by SSO using miniOrange Console, and is then redirected to his Crowd account.
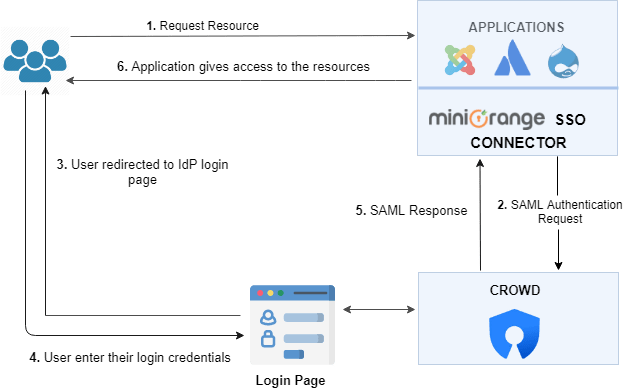
Crowd As Identity Provider Usecase
miniorange Single Sign-On plugin can use Crowd as Identity Provider. The miniOrange Single Sign-On(SSO) plugin forwards user authentication requests to Crowd. After successful authorization using Crowd credentials, the user is given access to the requested resource.
Workflow:
1. An unknown user tries to access the resources.
2. miniOrange creates a SAML authentication request and sends it to the Crowd.
3. User is redirected to Crowd login page, where the user enters their credentials to authorize the application.
4. The Crowd Server authenticates the user and sends the SAML response to miniOrange.
5. Upon successful authentication, the user is given access to the site.
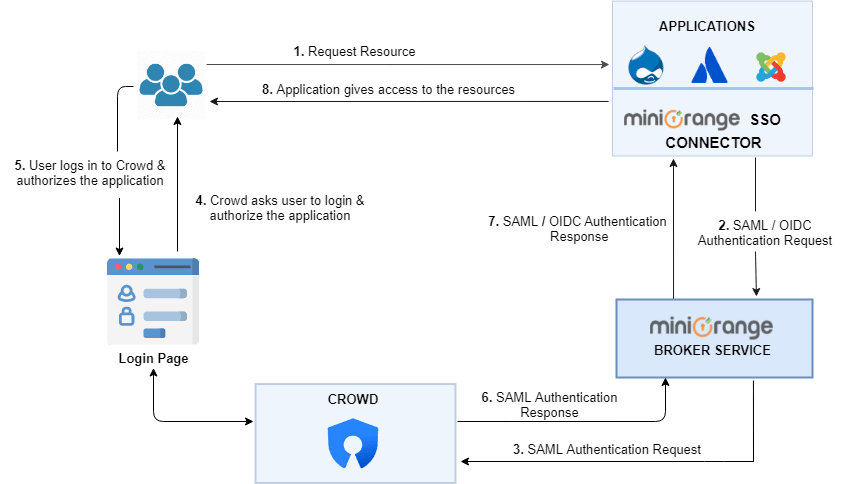
Crowd As User Store Usecase
With miniOrange Identity broker service you can delegate all your Single Sign-On(SSO) requirements, user management, Two factor authentication(2FA) and even risk based access at the click of a button and focus on your business case. We can integrate with any type of app even if it does not understand any standard protocol like SAML, OpenId Connect or OAuth. miniOrange Single Sign-On(SSO) Service can establish trust between two apps via secure https endpoint and automated user mapping to achieve SSO.
You can configure any User store like Crowd to Single Sign-On into applications which don’t support any protocol or supports protocols other than OAuth like SAML, WS-FED, JWT, etc. for Single Sign-On(SSO) using miniOrange cross-protocol support.
For example, you can configure the miniOrange broker service to use Crowd and single sign-on into an external application, such as Atlassian application like Jira, Bitbucket, Bamboo.
Workflow:
1. An unknown user tries to access any external application.
2. The Application sends an authentication request to miniOrange broker service, using SAML / OIDC protocol that the application supports.
3. The miniOrange broker service forwards the authentication request to Crowd.
4. User is redirected to Crowd login page, where the user enters their credentials to authorize the application.
5. The Crowd Server authenticates the user and sends the response to miniOrange broker service.
6. miniOrange broker service sends an authentication response to the Application. This response contains the user’s information as well as the authentication status, based on which the user is given access to the resource.
7. Upon successful authentication, the user is given access to the resource.
Users can Single Sign On into these apps using Crowd User Store credentials




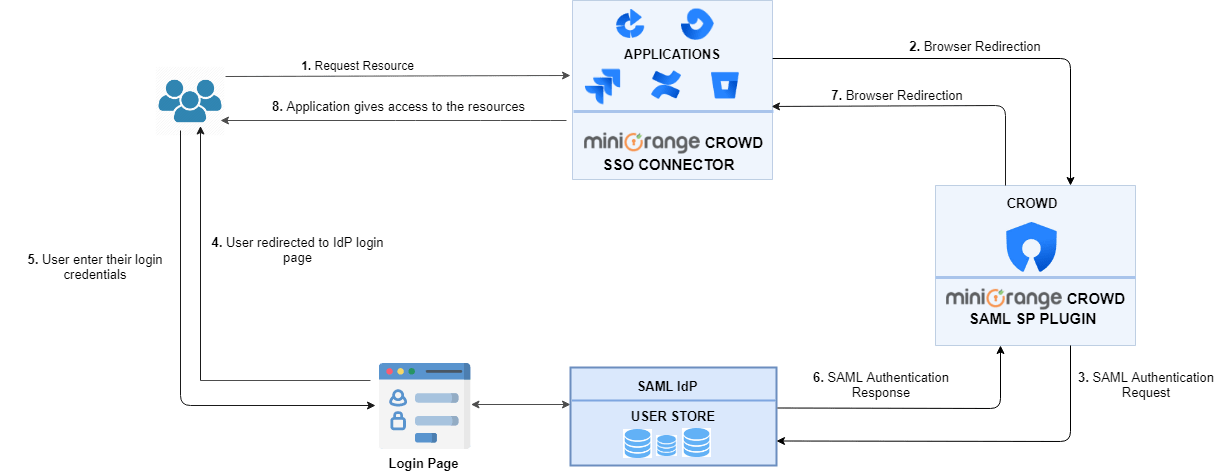
Crowd As Service Provider Usecase
Crowd can be configured to use any SAML Identity Provider. miniorange SAML Identity Provider for user authentication. When a user requests access for a resource, Crowd sends a SAML authentication request to miniOrange IdP and the user has to login with their miniOrange account. On successful authentication, the user is provided access to the resource.
Workflow:
1. An unknown user tries to access Atlassian Applications (Jira, Confluence, Bitbucket, Bamboo and Fisheye).
2. Crowd creates a SAML authentication Request and sends it to the configured Identity Provider. The user is prompted to log in with their Identity Provider account.
3. The SAML Identity Provider sends back a SAML Response to the Crowd application. This response contains the user’s information as well as the authentication status, based on which the user is given access to the resource.
4. Upon successful authentication, the user is given access to the application.